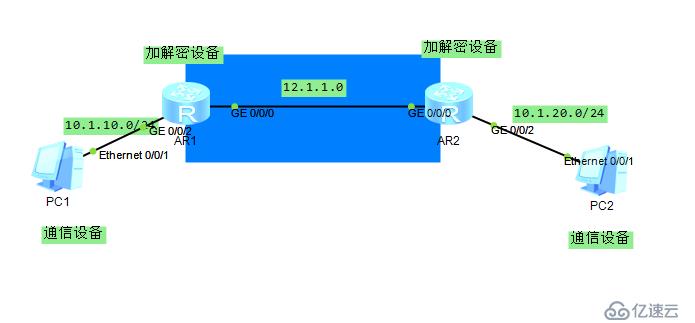
掌握华为设备上IKE方案实施站点到站点的虚拟私有网络(HCNP独家新增课程)
IPSec在IP层通过加密与数据来源认证等方式,来保证数据包在网络上传输时的私有性、真实性、完整性和抗重放。
IPSec加密和验证算法所使用的密钥可以手工配置,也可以通过因特网密钥交换IKE(Internet Key Exchange)协议动态协商。IKE协议建立在Internet安全联盟和密钥管理协议ISAKMP(Internet Security Association and Key Management Protocol)框架之上,采用DH(Diffie-Hellman)算法在不安全的网络上安全地分发密钥、验证身份,以保证数据传输的安全性。IKE协议可提升密钥的安全性,并降低IPSec管理复杂度。
目的
在Internet的传输中,绝大部分数据的内容都是明文传输的,这样就会存在很多潜在的危险,比如:密码、银行帐户的信息被窃取、篡改,用户的身份被冒充,遭受网络恶意×××等。网络中部署IPSec后,可对传输的数据进行保护处理,降低信息泄漏的风险。
受益
IPSec通过加密与验证等方式,从以下几个方面保障了用户业务数据在Internet中的安全传输:
数据来源验证:接收方验证发送方身份是否合法。
数据加密:发送方对数据进行加密,以密文的形式在Internet上传送,接收方对接收的加密数据进行解密后处理或直接转发。
数据完整性:接收方对接收的数据进行验证,以判定报文是否被篡改。
抗重放:接收方拒绝旧的或重复的数据包,防止恶意用户通过重复发送捕获到的数据包所进行的×××。
ip route-static 0.0.0.0 0.0.0.0 12.1.1.2 //该路由可以解决到达对端通信点以及对端加解密点的通信问题
这些流量将被×××做安全处理
acl number 3000
rule 5 permit ip source 10.1.10.0 0.0.0.255 destination 10.1.20.0 0.0.0.255
ipsec proposal 10
esp authentication-algorithm sha2-384
esp encryption-algorithm aes-128
ike proposal 10
encryption-algorithm aes-cbc-128
dh group2
ike peer R2 v1
pre-shared-key simple qytang
ike-proposal 10
remote-address 12.1.1.2
ipsec policy P1 10 isakmp
security acl 3000
ike-peer R2
proposal 10
interface GigabitEthernet0/0/0
ip address 12.1.1.1 255.255.255.0
ipsec policy P1
AR2的配置几乎和AR1相同,大部分内容比如acl将流量的源目对调即可,请参考如下配置
acl number 3000
rule 5 permit ip source 10.1.20.0 0.0.0.255 destination 10.1.10.0 0.0.0.255
#
ipsec proposal 10
esp authentication-algorithm sha2-384
esp encryption-algorithm aes-128
#
ike proposal 10
encryption-algorithm aes-cbc-128
dh group2
#
ike peer R1 v1
pre-shared-key simple qytang
ike-proposal 10
remote-address 12.1.1.1
#
ipsec policy P1 10 isakmp
security acl 3000
ike-peer R1
proposal 10
#
interface GigabitEthernet0/0/0
ip address 12.1.1.2 255.255.255.0
ipsec policy P1
#
interface GigabitEthernet0/0/2
ip address 10.1.20.254 255.255.255.0
#
ip route-static 0.0.0.0 0.0.0.0 12.1.1.1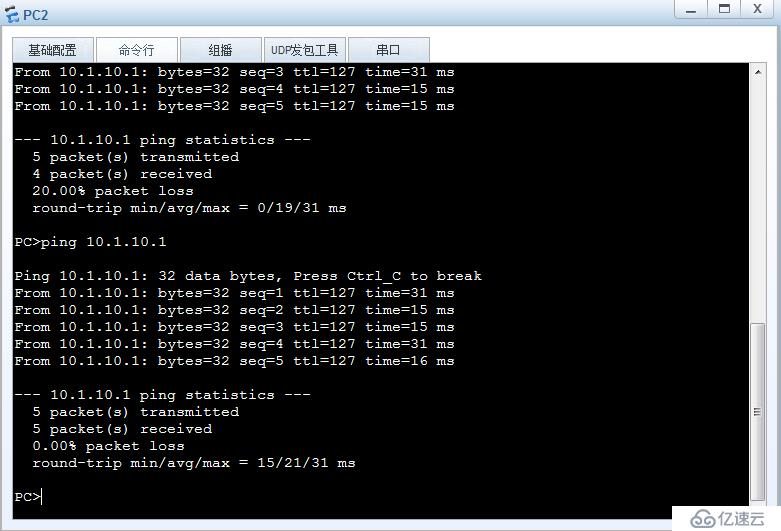
验证:
[Gateway1]display ike sa
Conn-ID Peer ××× Flag(s) Phase
---------------------------------------------------------------
2 12.1.1.2 0 RD|ST 2
1 12.1.1.2 0 RD|ST 1
Flag Description:
RD--READY ST--STAYALIVE RL--REPLACED FD--FADING TO--TIMEOUT
HRT--HEARTBEAT LKG--LAST KNOWN GOOD SEQ NO. BCK--BACKED UP
[Gateway1]dis ike peer
Number of IKE peers: 1
Peer name Exchange Remote NAT
mode name traversal
-------------------------------------------------------
R2 Main Disable
[Gateway1]dis ike statistics v1
----------------------------------------------------------
IKE V1 statistics information
Number of total peers : 18
Number of policy peers : 1
Number of profile peers : 17
Number of proposals : 2
Number of established V1 phase 1 SAs : 1
Number of established V1 phase 2 SAs : 1
Number of total V1 phase 1 SAs : 1
Number of total V1 phase 2 SAs : 1
Number of total SAs : 2
Keep alive time : 0
Keep alive interval : 0
keepalive spi list : Disable
----------------------------------------------------------
[Gateway1]dis ipsec sa // 查看IPSEC SA,它用于确定网络的两侧,同时进行数据加解密
===============================
Interface: GigabitEthernet0/0/0
Path MTU: 1500
===============================
-----------------------------
IPSec policy name: "P1"
Sequence number : 10
Acl Group : 3000
Acl rule : 5
Mode : ISAKMP
-----------------------------
Connection ID : 2
Encapsulation mode: Tunnel
Tunnel local : 12.1.1.1
Tunnel remote : 12.1.1.2
Flow source : 10.1.10.0/255.255.255.0 0/0
Flow destination : 10.1.20.0/255.255.255.0 0/0
Qos pre-classify : Disable
[Outbound ESP SAs]
SPI: 1214314935 (0x4860f9b7)
Proposal: ESP-ENCRYPT-AES-128 SHA2-384-192
SA remaining key duration (bytes/sec): 1887283200/3079
Max sent sequence-number: 10
UDP encapsulation used for NAT traversal: N
[Inbound ESP SAs]
SPI: 2003986867 (0x777269b3)
Proposal: ESP-ENCRYPT-AES-128 SHA2-384-192
SA remaining key duration (bytes/sec): 1887436260/3079
Max received sequence-number: 9
Anti-replay window size: 32
UDP encapsulation used for NAT traversal: N
[Gateway1]dis ipsec policy
===========================================
IPSec policy group: "P1"
Using interface: GigabitEthernet0/0/0
===========================================
Sequence number: 10
Security data flow: 3000
Peer name : R2
Perfect forward secrecy: None
Proposal name: 10
IPSec SA local duration(time based): 3600 seconds
IPSec SA local duration(traffic based): 1843200 kilobytes
Anti-replay window size: 32
SA trigger mode: Automatic
Route inject: None
Qos pre-classify: Disable
[Gateway1]dis ipsec statistics esp
Inpacket count : 9
Inpacket auth count : 0
Inpacket decap count : 0
Outpacket count : 10
Outpacket auth count : 0
Outpacket encap count : 0
Inpacket drop count : 0
Outpacket drop count : 0
BadAuthLen count : 0
AuthFail count : 0
InSAAclCheckFail count : 0
PktDuplicateDrop count : 0
PktSeqNoTooSmallDrop count: 0
PktInSAMissDrop count : 0需要注意的是ensp的acl并不一定匹配,如下所示
<Gateway1>dis acl all
Total quantity of nonempty ACL number is 1
Advanced ACL 3000, 1 rule
Acl's step is 5
rule 5 permit ip source 10.1.10.0 0.0.0.255 destination 10.1.20.0 0.0.0.255
下图帮您认识ESP报文,您不能在看到icmp报文,因为数据被加密处理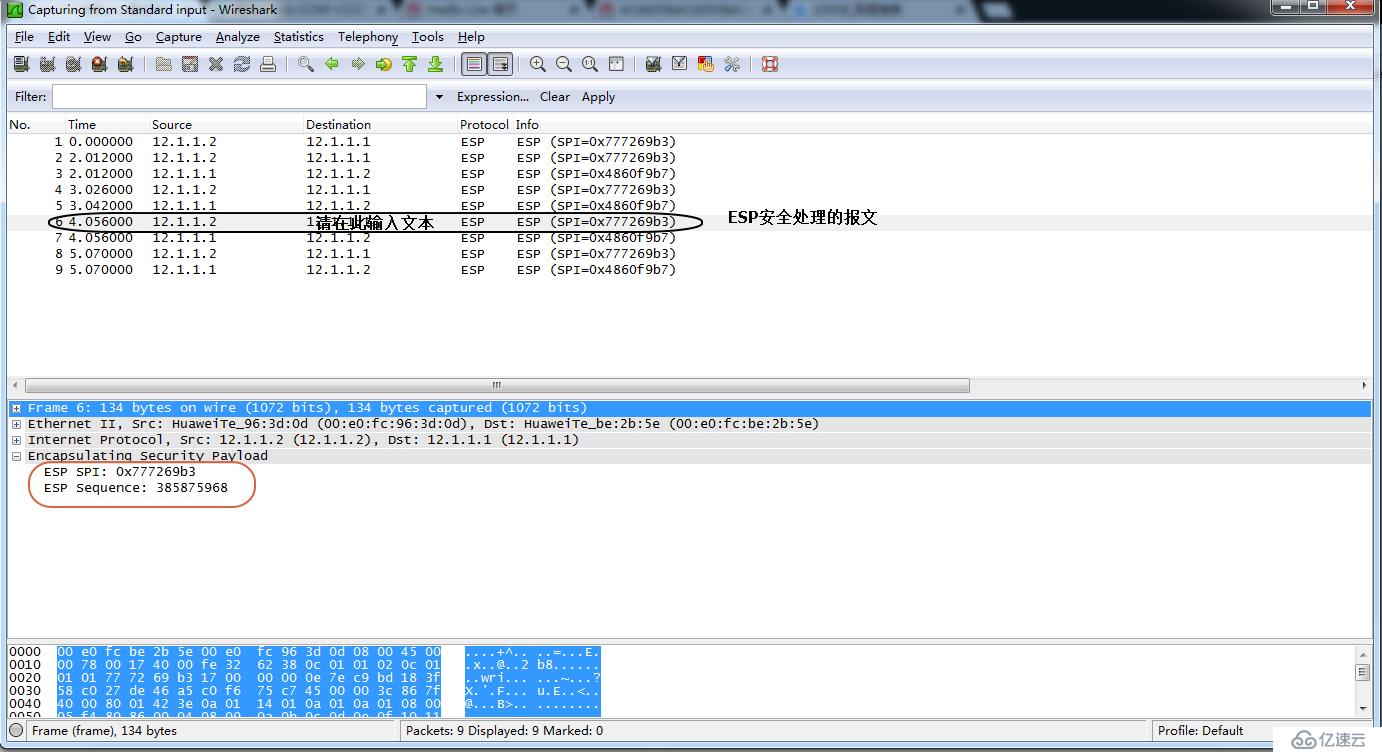
免责声明:本站发布的内容(图片、视频和文字)以原创、转载和分享为主,文章观点不代表本网站立场,如果涉及侵权请联系站长邮箱:is@yisu.com进行举报,并提供相关证据,一经查实,将立刻删除涉嫌侵权内容。