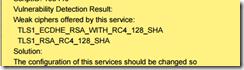
先看看扫描到的漏洞截图


下面是详细的操作解决方案(以下的配置经过了多次的修改才将漏洞真正修复完毕):
安全配置一:
[root@liulingli html]# find / -name .htaccess
/var/www/html/wp-content/cache/autoptimize/.htaccess
vim /var/www/html/wp-content/cache/autoptimize/.htaccess
添加如下5行
<IfModule mod_rewrite.c>
RewriteEngine on
RewriteCond %{REQUEST_METHOD}^(TRACE|TRACK)
RewriteRule .*-[F]
</ifModule>
重启httpd服务
[root@liulingli html]# service httpd restart
Stopping httpd: [ OK ]
Starting httpd: [ OK ]
安全配置二:
echo "net.ipv4.tcp_timestamps = 0" >> /etc/sysctl.conf
sysctl -p
安全配置三:
vim /etc/httpd/conf.d/ssl.conf
原来的配置
# SSL Protocol support:
# List the enable protocol levels with which clients will be able to
# connect. Disable SSLv2 access by default:
SSLProtocol all -SSLv2
# SSL Cipher Suite:
# List the ciphers that the client is permitted to negotiate.
# See the mod_ssl documentation for a complete list.
SSLCipherSuite ALL:!ADH:!EXPORT:!SSLv2:RC4+RSA:+HIGH:+MEDIUM:+LOW
修改成以下配置:
SSLProtocol all -SSLv2 -SSLv3
# SSL Cipher Suite:
# List the ciphers that the client is permitted to negotiate.
# See the mod_ssl documentation for a complete list.
SSLHonorCipherOrder on
SSLCipherSuite ECDHE-RSA-AES256-GCM-SHA384:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-RSA-AES256-SHA384:ECDHE-RSA-AES128-SHA256:ECDHE-RSA-RC4-SHA:ECDHE-RSA-AES256-SHA:DHE-RSA-AES256-SHA:DHE-RSA-AES128-SHA:RC4-SHA:!aNULL:!MD5:!DSS:!RC4
并且添加以下三行
RewriteEngine on
RewriteCond %{REQUEST_METHOD} ^(TRACE|TRACK)
RewriteRule .* - [F]
</VirtualHost>
service httpd restart
注意}后面有空格,否则无法重启httpd服务
再次对网站进行扫描,发现高危和中危漏洞警报都已经消除。

经过了10次修改和扫描,才最终解决。

免责声明:本站发布的内容(图片、视频和文字)以原创、转载和分享为主,文章观点不代表本网站立场,如果涉及侵权请联系站长邮箱:is@yisu.com进行举报,并提供相关证据,一经查实,将立刻删除涉嫌侵权内容。